InSight is eKare’s Cloud Based wound management solution built on a certified secure platform and proven core technologies and software architectures that follow best practices and meet current local, federal and international health information privacy and information security policies.
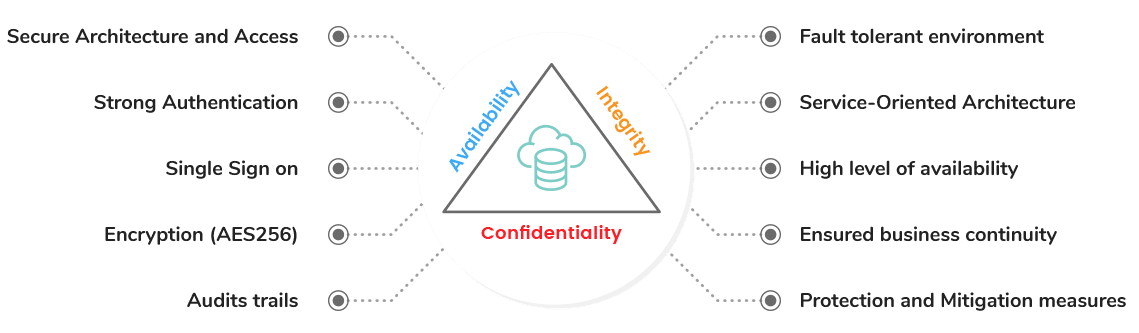
Our advanced security principles align with the CIA triad
inSight’s telehealth capabilities deliver convenient and secure solutions for healthcare providers to remotely monitor wound care patients. Our workflow enables patient participation, allowing them to easily photograph and submit wound images, complete wound assessments and chat securely with their provider. Clinicians have the ability to conveniently access patient captured data, communicate directly with their patients, and securely store & forward data to the wound care team to advance outcomes. Contact info@ekare.ai for details on eKare’s Security Policy.